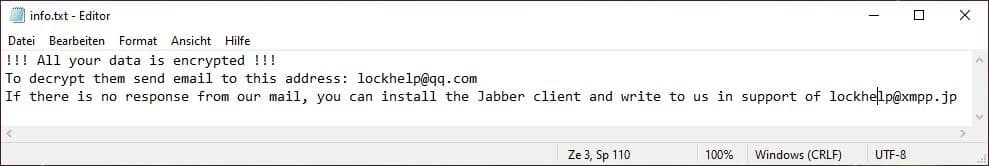
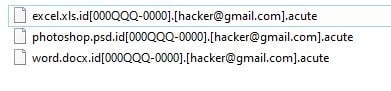
If you get hit by Phobos ransomware, you may have an emergency on your hands. Still, it’s important to stay calm. You can learn more about the Phobos ransomware and how to identify it and remove it on this page. For personalized assistance, you can also contact our team of ransomware data recovery experts 24/7 and for a FREE consultation and immediate assessment of the damages.
We work with clients all over the world, so wherever you are located, we can help. Our team consists of highly specialized German technicians, and can help you recover your precious data with a quick and painless ransomware removal and remediation process.