GlobeImposter 2.0 Ransomware: Sofortige Maßnahmen und schnelle Wiederherstellungsmöglichkeiten
Wurden Sie von GlobeImposter 2.0 Ransomware getroffen? Bewahren Sie Ruhe. Wir sind hier, um Ihnen zu helfen. Diese Seite enthält Informationen und Statistiken zur Entschlüsselung, Entfernung und Wiederherstellung von GlobeImposter 2.0 Ransomware. Lesen Sie weiter, um mehr zu erfahren, oder kontaktieren Sie uns jetzt für eine KOSTENLOSE Bewertung Ihrer Situation.
Was ist GlobeImposter 2.0 Ransomware?
Mit rapider Verschlüsselung und unerbittlichen Erpressungsmethoden zielt GlobeImposter 2.0 auf Unternehmen jeder Größenordnung ab. Erfahren Sie, wie diese Ransomware funktioniert, betrachten Sie reale Angriffe und erhalten Sie fachkundige Unterstützung, um Ihre Dateien wiederherzustellen und den Normalbetrieb wiederaufzunehmen.
Verschlüsselung von Netzwerkfreigaben
Verschlüsselt Dateien über freigegebene Laufwerke und Server hinweg, um die betriebliche Störung zu maximieren.Persistenzmechanismen
Installiert versteckte Werkzeuge, um langfristigen Zugriff aufrechtzuerhalten und Systeme erneut zu infizieren.Warum Sie nicht versuchen sollten, es alleine zu beheben
Wenn Ihr Unternehmen von GlobeImposter 2.0 Ransomware betroffen ist, können falsche Schritte zu permanentem Datenverlust
oder rechtlichen Risiken führen. Ähnlich einem Tatort muss ein Ransomware-Angriff bewahrt werden – eine Manipulation
verschlüsselter Dateien, eigenständige Wiederherstellungsversuche oder Kommunikation mit den Angreifern können
entscheidende Beweise zerstören und Ihre Wiederherstellungschancen mindern.
Die richtige Reaktion in den ersten Momenten nach einem GlobeImposter 2.0-Angriff kann den Unterschied
zwischen vollständiger Wiederherstellung und dauerhaftem Datenverlust ausmachen. Befolgen Sie diese kritischen Schritte, um Ihre
Daten zu schützen und Ihre Chancen auf Wiederaufnahme des Betriebs zu maximieren.
Was sollte ich tun, wenn meine Daten von GlobeImposter 2.0 Ransomware verschlüsselt wurden?
Wenn Sie Opfer von Ransomware geworden sind, befolgen Sie diese entscheidenden Schritte:
24/7 Ransomware-Wiederherstellungshilfe anfordern
Erhalten Sie Expertenberatung zur sicheren Bewertung, Eindämmung und Wiederherstellung.
Infizierte Systeme isolieren
Trennen Sie infizierte Geräte, um die Ausbreitung zu stoppen. Vermeiden Sie Selbstwiederherstellungsversuche.
Beweise sofort sichern
Bewahren Sie Erpresserschreiben Protokolle auf. Starten Sie nichts neu und modifizieren Sie nichts.
GlobeImposter 2.0 Ransomware Statistiken Fakten
LÖSEGELDBETRÄGE
Diverse Gruppen verwenden GlobeImposter 2.0 Ransomware, daher können die Lösegeldforderungen variieren.
DURCHSCHNITTLICHE DAUER
Die Ausfallzeit durch GlobeImposter 2.0 Ransomware kann in der Regel kürzer sein als bei normalen Ransomware-Angriffen. Dies liegt daran, dass die meisten GlobeImposter 2.0 Angreifer eine automatisierte TOR-Seite verwenden, um die Zahlung zu akzeptieren und das Entschlüsselungstool zu liefern.
Abhängig von der Größe Ihres Unternehmens und der Häufigkeit der Nutzung von IT-Systemen in Ihrem Tagesgeschäft stellt dies den kostspieligsten Teil dieses Vorfalls dar. Zusätzlich zur Nichtverfügbarkeit Ihrer IT-Systeme schädigt dies den Ruf Ihres Unternehmens.
Ihr Ziel sollte es sein, Ihre Systeme so schnell wie möglich wieder in einen produktiven Zustand zu bringen. Der beste Weg, dies zu erreichen, ist, Experten hinzuzuziehen, die über umfangreiches Wissen über GlobeImposter 2.0 Ransomware verfügen und die IT-Systeme wieder zum Laufen bringen.
FALLAUSGÄNGE
Es besteht eine hohe Wahrscheinlichkeit, nach der Zahlung an die Angreifer einen funktionierenden GlobeImposter 2.0 Entschlüsseler zu erhalten. Es gibt jedoch nie eine Garantie.
Einige Angreifer haben einen guten Ruf für die Bereitstellung funktionierender GlobeImposter 2.0 Entschlüsseler. Andere sind bekannte Betrüger und werden nie einen zur Verfügung stellen.
HÄUFIGE ANGRIFFSVEKTOREN
Der häufigste Angriffsvektor für GlobeImposter 2.0 Ransomware sind Spam-E-Mails und infizierte Webseiten.

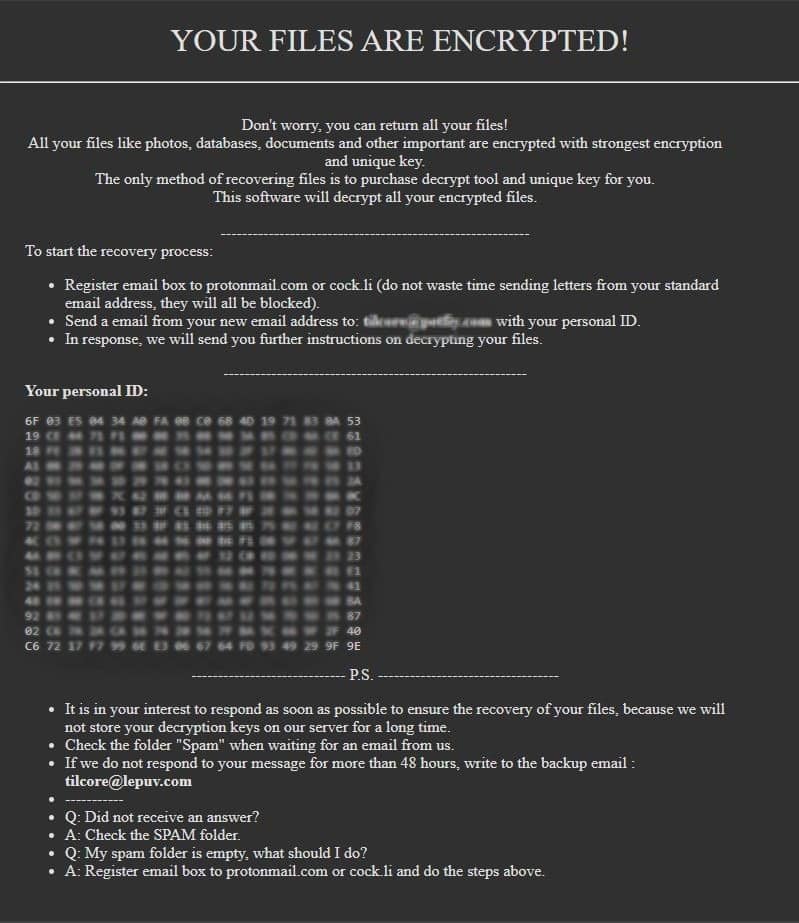
Wie man GlobeImposter 2.0 Ransomware identifiziert
Dies ist eine durchschnittliche GlobeImposter 2.0 Ransomware-Mitteilung. (Mit leichter Redaktion im Interesse der öffentlichen Sicherheit)
GlobeImposter 2.0 Entschlüsselungs-Demonstration
Dies ist eine technische Demonstration des GlobeImposter 2.0 Entschlüsselungsprogramms. Urheberrechtlich geschützt durch BeforeCryptErleben Sie einen Ransomware-Angriff oder eine Cybersicherheitsverletzung?
Jetzt Hilfe anfordernHäufig gestellte Fragen
Die Entschlüsselung hängt von der jeweiligen Ransomware-Variante ab. In einigen Fällen gibt es öffentlich verfügbare Entschlüsselungstools, aber nicht jeder Angriff hat eine bekannte Lösung. Sie können eine kostenlose Anfrage zur Ransomware-Wiederherstellung einreichen, und wir prüfen mögliche Entschlüsselungsmethoden.