GlobeImposter 2.0 Ransomware: Immediate Steps to Take & How to Recover Quickly
Did you get hit by GlobeImposter 2.0 ransomware? Don’t panic. We’re here to help. This page contains information and statistics about GlobeImposter 2.0 ransomware decryption, removal, and recovery. Read on to find out more, or get in touch with us now and for a FREE assessment of your situation.
What is GlobeImposter 2.0 Ransomware?
With rapid encryption and relentless extortion methods, GlobeImposter 2.0 targets companies big and small. Learn how this ransomware works, explore real-world attacks, and get expert support to restore your files and get back on track.
Encryption of Network Shares
Encrypts files across shared drives and servers to maximize operational disruption.Persistence Mechanisms
Installs hidden tools to maintain long-term access and re-infect systems.Why You Shouldn’t Attempt to Fix It Alone
If GlobeImposter 2.0 ransomware has hit your business, taking the wrong steps can cause permanent data
loss or legal risks. Like a crime scene, a ransomware attack must be preserved—tampering
with encrypted files, attempting self-recovery, or engaging with attackers can destroy
critical evidence and reduce your chances of recovery.
The right response in the first moments after a GlobeImposter 2.0 attack can make the difference
between full recovery and permanent data loss. Follow these critical steps to protect your
data and maximize your chances of restoring operations.
What should I do when my data has been encrypted by GlobeImposter 2.0 Ransomware?
If you’ve fallen victim to ransomware, follow these crucial steps:
Request 24/7 Ransomware Recovery Help
Get expert guidance to assess, contain, and recover safely.
Isolate Infected Systems
Disconnect infected devices to stop the spread. Avoid self-recovery.
Preserve Evidence Immediately
Keep ransom notes & logs. Do not restart or modify anything.
GlobeImposter 2.0 ransomware statistics & facts
RANSOM AMOUNTS
Diverse groups use GlobeImposter 2.0 ransomware, so ransom amounts may vary.
The average GlobeImposter 2.0 ransom amount is somewhere between $7,500 – $70,000. If you purchase Bitcoin to pay this, you will need to add 10% to cover the quick-buy method fees if you are purchasing with a credit card or PayPal on an exchange.
AVERAGE LENGTH
The GlobeImposter 2.0 ransomware downtime can usually be shorter than normal ransomware attacks. This is because most GlobeImposter 2.0 attackers use an automated TOR site to accept payment and deliver the decryption tool.
Depending on your company size and how often you use IT-systems in your daily business, this is the most expensive part of this incident. Additional to the unavailability of your IT-systems, this is damaging your company reputation.
Your goal should be to get your systems back to a productive state as soon as possible. The best way to do this is to call in experts, which have a vast knowledge of GlobeImposter 2.0 ransomware and get the IT-systems back up running.
CASE OUTCOMES
There is a high chance of getting a working GlobeImposter 2.0 decryptor after paying the attackers. But there’s never a guarantee.
Some attackers have a good reputation for providing working GlobeImposter 2.0 decryptors. Others are known scammers and will never provide one.
COMMON ATTACK VECTORS
The most common attack vector for GlobeImposter 2.0 ransomware is spam emails and contagious webpages.

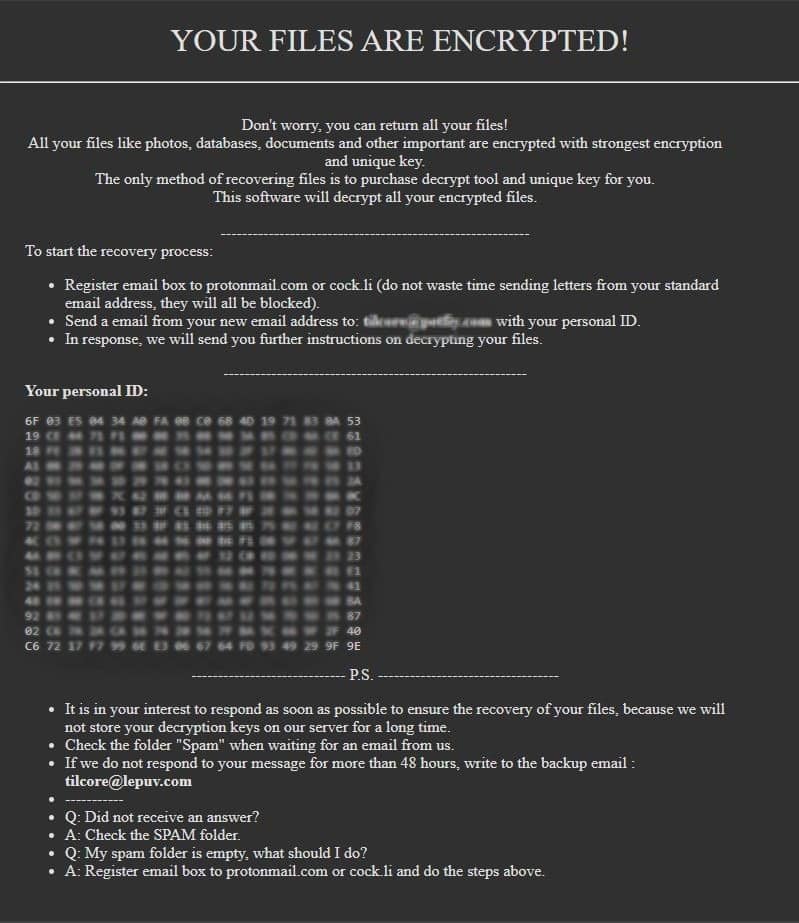
How to identify GlobeImposter 2.0 ransomware
This is an average GlobeImposter 2.0 ransomware note. (With slight redaction in the interest of public safety)
GlobeImposter 2.0 decryptor demonstration
This is a technical demo of the GlobeImposter 2.0 Decryptor. Copyright by BeforeCryptExperiencing Ransomware or Cyber Breach?
Get Help NowFrequently asked questions
Decryption depends on the ransomware variant. In some cases, publicly available decryption tools exist, but not all attacks have a known solution. You can submit a free ransomware recovery request, and we will check for possible decryption methods.