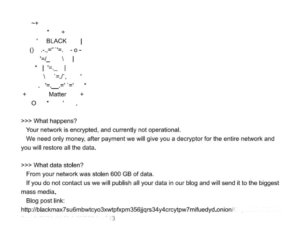
BlackMatter recently made headlines by compromising the networks of Japanese medical imaging giant Olympus. The group is trying to keep a low profile, though, after DarkSide’s attack on the Colonial pipeline attracted a lot of heat, including a hack by the US government in which part of the ransom was seized.
The gang publicly announced they would not be targeting any critical infrastructure or hospitals, presumably because it’s trying to avoid unwanted attention.
The Evolution of Ransomware
BlackMatter represents a merger of some of the most potent technologies currently active in the ransomware threat landscape.
Experts see many similarities between BlackMatter and Darkside, but it also incorporates features from REvil, making it an even more potent virus. However, there are some important differences that indicate BlackMatter may be more than just a DarkSide rebrand. For example, BlackMatter targets Russian companies, which was off limits for DarkSide. Some sources on the dark web suggest that DarkMatter sold off the source code to whoever is now operating BlackMatter.
BlackMatter also has both WIndows and Linux versions, as opposed to most ransomware outfits that mainly target Windows. This means BlackMatter is a greater threat to servers, which mostly run Linux.
Blackmatter features an impressive suite of features that help prevent detection by antivirus software. BlackMatter, like DarkSide, stores configuration information in encrypted binary, making it much more difficult to detect. It also has a runtime API used for evading malware analysis. This doesn’t make it harder to detect, but it makes it much more difficult for antivirus software developers to develop countermeasures for detecting and stopping BlackMatter. BlackMatter also uses import and string obfuscation.
Things to watch for with BlackMatter Ransomware
Victims that pay the ransom have al gotten working decryptors so far, but there’s a few things to watch for. For example, one of BlackMatter’s unique features is that it changes file permissions so that anyone can access certain files. This is part of the process of infiltrating and encrypting the network, but decrypting the files will not change the file permissions back. For this reason, it’s important to review file permissions before getting back to work.
It can be helpful to be aware that BlackMatter attacks frequently use Cobalt Strike. Monitoring for Cobalt Strike C2 servers can be helpful in detecting and moving to prevent BlackMatter attacks.
BlackMatter is very keen to use sensitive data for extortion. Ideally, organizations that store sensitive data should use an encrypted, air gapped storage medium to prevent attackers from gaining access.
BlackMatter is also aggressively pursuing “inside” attack vectors. In other words, they seek out disgruntled or unscrupulous employees, and offer to pay them a share of the ransom in exchange for access to an organization’s network. This represents a new attack vector to protect against.
The Future of BlackMatter
BlackMatter definitely represents the cutting edge of ransomware. Hackers are making so much money now that they are able to outspend cybersecurity experts, meaning ransomware is able to stay one step ahead of threat detection.
If cybersecurity doesn’t see major investments soon, we can expect to see more devastating BlackMatter attacks in the coming months.
If BlackMatter ransomware infects your networks, we can help. Contact us for a free ransomware recovery consultation to learn more about the best way to handle a BlackMatter attack.
You are currently viewing a placeholder content from Wistia. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information