Dharma Ransomware Recovery and Removal Experts
Has Dharma Ransomware held your company’s files hostage? If files have encrypted with a .DHARMA extension and backups failed, it is a highly critical situation. Do not hesitate, we’re here to help you. This page provides detailed information in regards to Dharma ransomware, decryption, recovery, removal and statistics. Contact us now to help you in recovering from a Dharma Ransomware Attack.
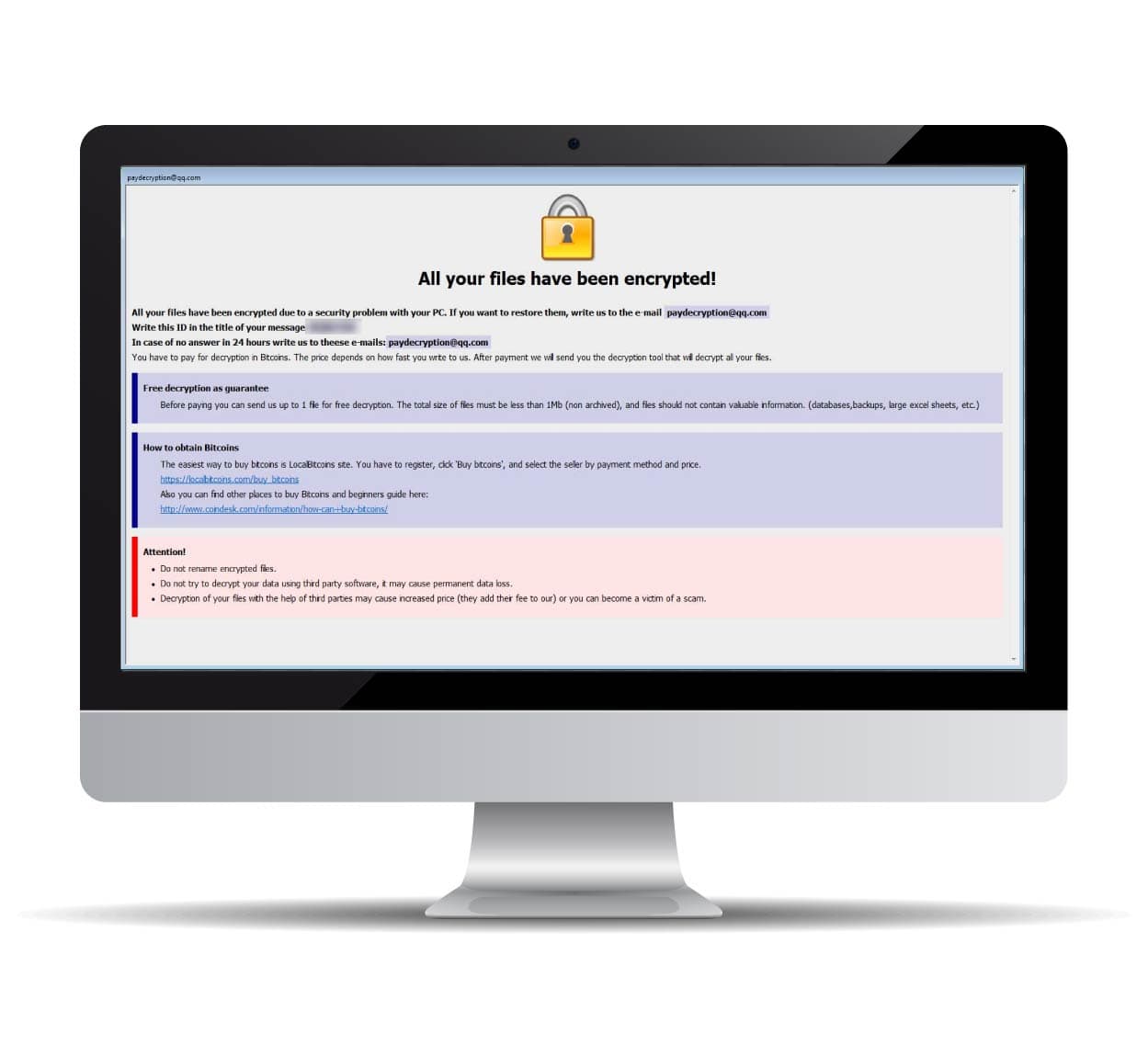
How do I know if our company has been hit with Dharma Ransomware?
A Dharma Encryption payload is a so-called Ransomware Trojan that encrypts an entire PC or a plethora if not all machines on your network. First discovered roundabout the 21st of October, 2017, Dharma Ransomware was originally known as Crysis and had a close relationship to XTBL. Once files are encrypted, hackers proceed to demand a bitcoin payment to remove the ransomware encryption.
There are over 30 variants of the virus with a number of file extensions such as .BMP, .BIP, and .COMBO among many others.
Just like most other ransomware variants, Dharma is most commonly spread via an open RDP (Remote Desktop Protocol) port, either through the use of various exploits and vulnerabilities inherent to Remote Desktop of through dictionary or brute force attacks. Once access is gained by the attackers, various methods are employed to spread laterally such as the use of Mimikatz to gain administrative access or control over more machines within the network. All the while the attackers poise themselves to launch their encryption at the opportune time whilst monitoring company activities to determine value and perfect their strategy.
What should I do when my data has been encrypted by Dharma Ransomware?
If you’ve fallen victim to ransomware, follow these crucial steps:
Request 24/7 Ransomware Recovery Help
Get expert guidance to assess, contain, and recover safely.
Isolate Infected Systems
Disconnect infected devices to stop the spread. Avoid self-recovery.
Preserve Evidence Immediately
Keep ransom notes & logs. Do not restart or modify anything.
Dharma ransomware statistics & facts
RANSOM AMOUNTS
The nature of a Dharma Ransomware attack is different depending on the hacker or hacker group behind the attack. This amounts to varying degrees of ransom amounts that each hacker or group charges.
The average Dharma ransom amount is somewhere between $2,000–$8,000. However, over the last year, the average amount has begun to exceed $8,000. In addition, approximately 10% of Bitcoin exchange fees will apply to the use of quick-buy methods such as PayPal or credit card.
AVERAGE LENGTH
The Dharma ransomware downtime is a bit longer than normal ransomware attacks. The manual process of email-based communication with the attackers can add a considerable delay in the response time.
Depending on your company size and how often you use IT-systems in your daily business, this is the most expensive part of this incident. Additional to the unavailability of your IT-systems, this is damaging your company reputation.
Your goal should be to get your systems back to a productive state as soon as possible. The best way to do this is to call in experts, which have a vast knowledge of Dharma ransomware and get the IT-systems back up running.
CASE OUTCOMES
There is a high chance to get a working Dharma decryptor after paying the attackers. But there’s never a guarantee to get a working decryption key at all.
Depending on the file extension and email address of the attackers, there are different chances of getting a working Dharma decryptor after payment.
Some attackers have a good reputation for providing working Dharma decryptors. Others are known as scammers and will never give a Dharma decryptor.
COMMON ATTACK VECTORS
The most common attack vector for Dharma ransomware is an unsecured RDP-Connection (Remote Desktop Protocol). Followed up by phishing emails and security vulnerabilities.
2- [email protected] (IN PROGRESS)
3- [email protected] (EMAIL ACCOUNT SUSPENDED)
4- [email protected] (IN PROGRESS)
5- [email protected] (EMAIL ACCOUNT SUSPENDED)
6- [email protected] (CLOSED AUTOMATICALLY SINCE 06/05/2019 ACCORDING TO EMAIL SERVICE PROVIDER)
7- [email protected] (DOMAIN IS SUSPENDED SO EMAIL ACCOUNT IS DISABLED)
8- [email protected] (EMAIL ACCOUNT SUSPENDED)
9- [email protected] (EMAIL ACCOUNT CLOSED)
10- [email protected] (IN PROGRESS)
11- [email protected] (EMAIL ACCOUNT SUSPENDED)
12- [email protected] (IN PROGRESS)
13- [email protected] (EMAIL ACCOUNT DISABLED)
14- [email protected] (EMAIL ACCOUNT DISABLED)
15- [email protected] (EMAIL ACCOUNT DISABLED)
16- [email protected] (EMAIL ACCOUNT SUSPENDED)
17- [email protected] (IN PROGRESS)
18- [email protected] (EMAIL ACCOUNT SUSPENDED)
19- [email protected] (EMAIL ACCOUNT SUSPENDED)
20- [email protected] (IN PROGRESS)
21- [email protected] (IN PROGRESS)
22- [email protected] (IN PROGRESS)
23- [email protected] (EMAIL ACCOUNT SUSPENDED)
24- [email protected] (EMAIL ACCOUNT SUSPENDED)
25- [email protected] (EMAIL ACCOUNT SUSPENDED)
26- [email protected] (IN PROGRESS)
27- [email protected] (EMAIL ACCOUNT SUSPENDED)
28- [email protected] (EMAIL ACCOUNT SUSPENDED)
29- [email protected] (IN PROGRESS, same person as #32)
30- [email protected] (EMAIL ACCOUNT SUSPENDED, same person as #31)
31- [email protected] (IN PROGRESS, same person as #30)
32- [email protected] (EMAIL ACCOUNT SUSPENDED, same person as #29)
33- [email protected] (IN PROGRESS)
34- [email protected] or [email protected] (IN PROGRESS)
35- [email protected] (IN PROGRESS)
36- [email protected] (IN PROGRESS)
37- [email protected] (IN PROGRESS)
38- [email protected] (IN PROGRESS)
39- [email protected] (IN PROGRESS)
40- [email protected] (EMAIL ACCOUNT SUSPENDED)
41- [email protected] (IN PROGRESS)

How to identify Dharma ransomware
Dharma decryptor demonstration
Experiencing Ransomware or Cyber Breach?
Get Help NowFrequently asked questions
Decryption depends on the ransomware variant. In some cases, publicly available decryption tools exist, but not all attacks have a known solution. You can submit a free ransomware recovery request, and we will check for possible decryption methods.