eKing Ransomware: What You Need to Know & How to Recover Fast
eKing Ransomware is a highly aggressive ransomware strain, known for its fast encryption and extortion tactics against businesses of all sizes. Discover how it operates, review real-life cases, and get expert help to recover your data and resume operations.
What is Phobos Ransomware?
If you are unable to access your data, receive notice that your files have been encrypted, and see a demand for a ransom to regain access, it may mean your system is infected with eKing ransomware.
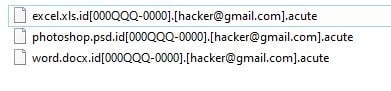
eKing Ransomware is a variant of the Phobos Ranswomare family and has been known to the cybersecurity community since August of 2021. Files encrypted by eKing generally have “eking” as a file extension. It uses both AES encryption standards. There is currently no known free decryptor for eKing.
Disables Backups
Actively seeks and deletes backups to prevent easy recovery after encryption.Spreads Through Networks
Targets entire IT infrastructures, not just single devices.Persistence Mechanisms
Installs hidden tools to maintain long-term access and re-infect systems.Why You Shouldn’t Attempt to Fix It Alone
If eKing ransomware has hit your business, taking the wrong steps can cause permanent data
loss or legal risks. Like a crime scene, a ransomware attack must be preserved—tampering
with encrypted files, attempting self-recovery, or engaging with attackers can destroy
critical evidence and reduce your chances of recovery.
The right response in the first moments after a eKing attack can make the difference
between full recovery and permanent data loss. Follow these critical steps to protect your
data and maximize your chances of restoring operations.
What should I do if and when my data has been encrypted by eKing?
If you’ve fallen victim to ransomware, follow these crucial steps:
Request 24/7 Ransomware Recovery Help
Get expert guidance to assess, contain, and recover safely.
Isolate Infected Systems
Disconnect infected devices to stop the spread. Avoid self-recovery.
Preserve Evidence Immediately
Keep ransom notes & logs. Do not restart or modify anything.
eKing ransomware statistics & facts
RANSOM AMOUNTS
The groups that operate eKing ransomware are known for targeting medium sized organizations. The gang is known to customize ransom demands based on the annual revenue of their victims.
The average eKing ransom amount ranges from $5,000-$30,000. Ransoms are usually paid in Bitcoin. Most quick-buy methods of purchasing Bitcoin via methods like PayPal or credit card will also apply a fee of up to 10%
AVERAGE LENGTH
The eKing ransomware downtime is a bit longer than other ransomware attacks. The manual process of email-based communication with the attackers can add a considerable delay in the response time.
Depending on your company size and how often you use systems in your day to day business, this is the most expensive part of this incident. Additional to the unavailability of your systems, this is damaging your company reputation.
Your goal should be to get your systems back to a productive state as soon as possible. The best way to do this is to call in experts, which have a vast knowledge of eKing ransomware and get the IT-systems back up running.
CASE OUTCOMES
In our experience, a successful ransom payment usually results in getting a working eKing decryptor. Decryptor tools do take work to maintain, however, so not all attackers have working tools.
It’s important to know which gang you are dealing with. Some attackers are careful to maintain a good reputation, and always provide working eKing decryptors. Others are known to be scammers, and will never provide a decryptor after receiving payment.
COMMON ATTACK VECTORS
The most common attack vector for eKing ransomware is phishing.

How to identify eKing ransomware
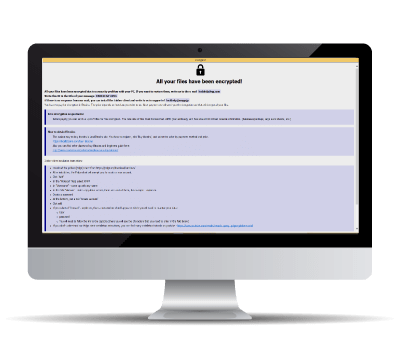
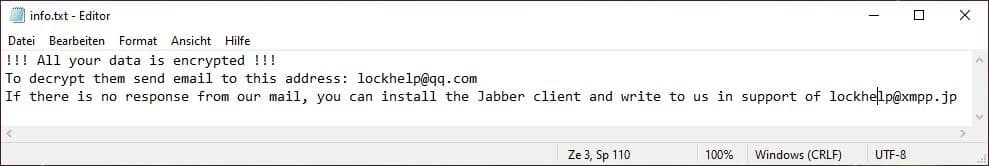
This is an average eKing ransomware note. (With slight redaction in the interest of public safety)
Typical screenshots of Phobos ransomware attacks
eKing decryptor demonstration
This is a technical demo of the eKing Decryptor. Copyright by BeforeCryptExperiencing Ransomware or Cyber Breach?
Get Help NowFrequently asked questions
Decryption depends on the ransomware variant. In some cases, publicly available decryption tools exist, but not all attacks have a known solution. You can submit a free ransomware recovery request, and we will check for possible decryption methods.