Before moving on, here’s some food for thought:
The Internet is equivalent to death for individuals and corporations who don’t know how to keep their identities, financial transactions, and data safe. For others, it’s a blessing!
In this guide, we will be exploring the difference between AES and RSA encryption, the industry-standards of encryption to secure data and minimize risk of loss.
What is encryption and how does it work?
Encryption is referred to securing the original data by masking and changing the entirety of information so that no unauthorized person can access it. This process generates a key, which is used to decrypt and get the data in its original form.
The entire idea is to ensure that only the original data owner with a verified key has access to the data.
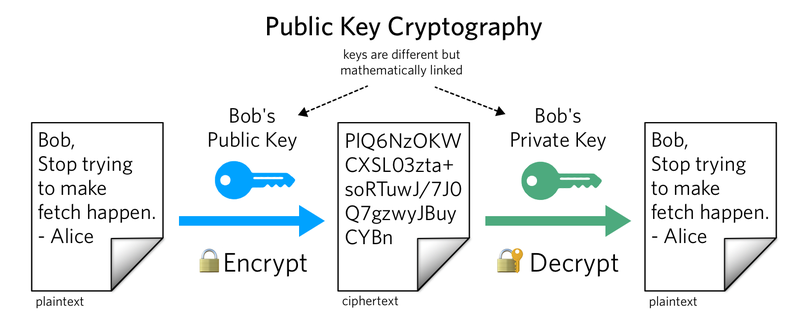
In encrypting and decrypting , you can either use symmetric or asymmetric keys. The former refers to the same key for encrypting and decrypting, whereas the latter is an encryption technology where the decryption key is different from the encryption key.
Today, we have two leading encryption standards used worldwide for safeguarding data, AES and RSA to secure data, and both have their own purposes.
What is AES encryption?
AES encryption, also known as Advanced Encryption Standard is the industry-leading, military-standard, symmetric encryption technology used to encrypt “top secret” data. The success of its encryption can be attributed to the fact that the National Security Agency (NSA) uses AES-256 bit encryption to secure top secret information of the country.
Figure 1. How AES Encryption works (Using a Single Key) Source
It gained prominence back in 1997, when NIST (National Institute of Standards and Technology) officially started researching for a faster, and securer encryption standard to replace the old and aging DES. Two Belgian cryptographists, Rijmen and Daemen were successful in developing an encryption standard that would be used as industry de-facto for years to come. In 2001, after rigorous testing and outstanding success rates, it was officially announced as a replacement for DES.
Since it is a symmetric algorithm, it uses the same 128, 192 or 256 bit key for encrypting and decrypting data. Due to the low computational power used to encrypt data, most of the modern laptops and smartphones can easily run it for data encryption.
As bits increase, so does the encryption power of AES. To give you an idea, it would take supercomputers of Google and several other tech giants, to work together, approximately over 77 billion years to crack 128 bits of data. Imagine how long would it take to crack a 256 bit AES encryption!
And so far, no system encrypted with AES has ever been cracked, which makes it the safest standard for governments, military units, and financial institutions worldwide!
What is RSA encryption?
RSA is named after three MIT scientists, Rivest, Shamir and Adleman that discovered the algorithm back in 1977, almost 2 decades before the discovery of AES.
It is an asymmetric encryption tool, which unlike AES, uses 2 encryption keys. One is a public key available to anyone, and the other is a private key only meant for the intended recipient of the data. Both are complementary in decrypting the data.
But what’s really interesting to note is how the RSA algorithm uses a mathematical formula to encrypt the data. i.e., factor integration. Data to be encrypted, is converted as one large number, raised to the key’s power, and divided with remainder by a fixed product of two primes. In short, the public key is a product of multiplication of two large numbers. And so far, the only possible way of decrypting the data is by knowing the 2 prime factors of the large number. So far, there is no known method of decrypting RSA over 768 bits in key length.
Encrypting data with RSA is a resource-consuming task, and not viable for most smartphones and laptops as it will slow down the devices. As such, it is used to encrypt only small amounts of data.
What happens if RSA or AES data is compromised?
Governments, military institutions, banks and intelligence agencies, classify, store and encrypt data mostly using AES. If AES is cracked and/or compromised in any way, the global economies would collapse. Banks would go bankrupt, national electricity grids could be turned off, etc. bringing the entire world to a complete standstill. So far, no data encrypted even with AES-128 bit has ever been cracked. It is for this reason, sensitive data is encrypted using AES. But the greater the key size, the secure the data is. Hence, it is always recommended to go with AES 128-bit or 256-bit in key length.
As such, whenever a ransomware attack happens, only criminals can decrypt your data as they have the decryptor tool.
But why a spike in ransomware attacks?
Well, here’s a bitter truth we want you to know. Because AES and RSA encryption are so hard to crack, criminals actually use the same encryption standards to encrypt YOUR data. Just imagine what would happen if a criminal gang gets hold of the nuclear launch codes, and threatens the government.
Let us put things into perspective for you. Let’s say:
All computers + supercomputers in the world combine to crack AES 512, it would take more than 77 billion years to do so. Even then, there is no guarantee that decryption would happen successfully!
This means that the very technology the military and governments use around the world to encrypt the data, is the one that hackers deploy to encrypt yours, lock the system and demand a hefty ransom. In this instance, only the attackers encrypting your data would have the key to decrypt it. Case closed!
Unfortunately, since no technology exists to break these encryption methods, the only option left in most cases is to let experts like BeforeCrypt to talk and deal with the attackers professionally. Although the FBI does NOT recommend paying ransom, we’d suggest otherwise only when it is absolutely necessary for your company to resume operations immediately.
Let’s have a comparison of the time taken to crack AES 128-bit vs AES 512-bit.
Cracking AES 128-bit:
Unlike the CPU speed measured in clocks, a supercomputer’s speed is measured in FLOPS (Floating point Operations Per Second).
On average, a supercomputer has the ability to perform 10.51 Petaflops = 10.51 x 1015 Flops
# of FLOPS required to crack every combination: Approx. 1000
# of combinations second = (10.51 x 1015 ) / 1000 = 10.51 x 1012
# seconds in a year = 365 * 24 * 60 * 60 = 31536000
# of years to crack AES 128-bit= (3.4 x 1038 ) / [(10.51 x 1012 ) x 31536000]
= (0.323 x 1026 )/31536000
= 1.02 x 1018
= 1 billion billion years
Cracking AES 512-bit:
If every person on the planet owns 10 computers, (10 * 7 billion= 70 billion computers) and each one of these computers can test 1 billion key combinations per second, it would take 77,000,000,000,000,000,000,000,000 years to crack one encryption key!
Let that sink in!
Many times, a ransomware attack shuts down the entire production and assembly lines, making thousands of workers redundant. By not paying the ransom, there is an even bigger risk of going bankrupt. We will help you to ensure that a deal is made where we negotiate and bring down the ransom amount to a reasonable level.
So, is paying a small ransom amount safer or shutting down the entire assembly line, and forcing thousands of workers out of job?
By the way, we have a complete first respondent guide on what to do in the event of a ransomware attack here.
But, how to ensure data safety?
Now that we all know what technology criminals use to encrypt your data (AES and RSA!), let’s talk about a complete holistic approach to data safety. We want you to jot down these points:
- Ensure you have a backup of data stored in a safe place alongside the latest versions of antivirus programs. Many ransomware are smartly designed to bypass any security such as firewall protection and antivirus programs, thereby directly encrypting the data.
- If you can, also have regular backups stored offline so in the event of an attack, you can safely restore them.
- Disable VSSAdmin and turn off all remote desktop sharing if you don’t need them. Most of these attacks come from leaving the remote desktop turned on.
- We all know just how pathetic the security of Windows operating systems is. Never rely on any open connections as you are simply inviting intruders, searching online for an open IP, to connect and hack your systems without you even knowing it.
Time and again, studies have proven that the end user is mostly responsible at times of ransomware attack, rather than the entire security architecture designed to keep the systems safe.
While there is always no guarantee of data safety even following all guidelines, at least you are minimizing the chances of getting your data compromised. Contact us for more information
You are currently viewing a placeholder content from Wistia. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information